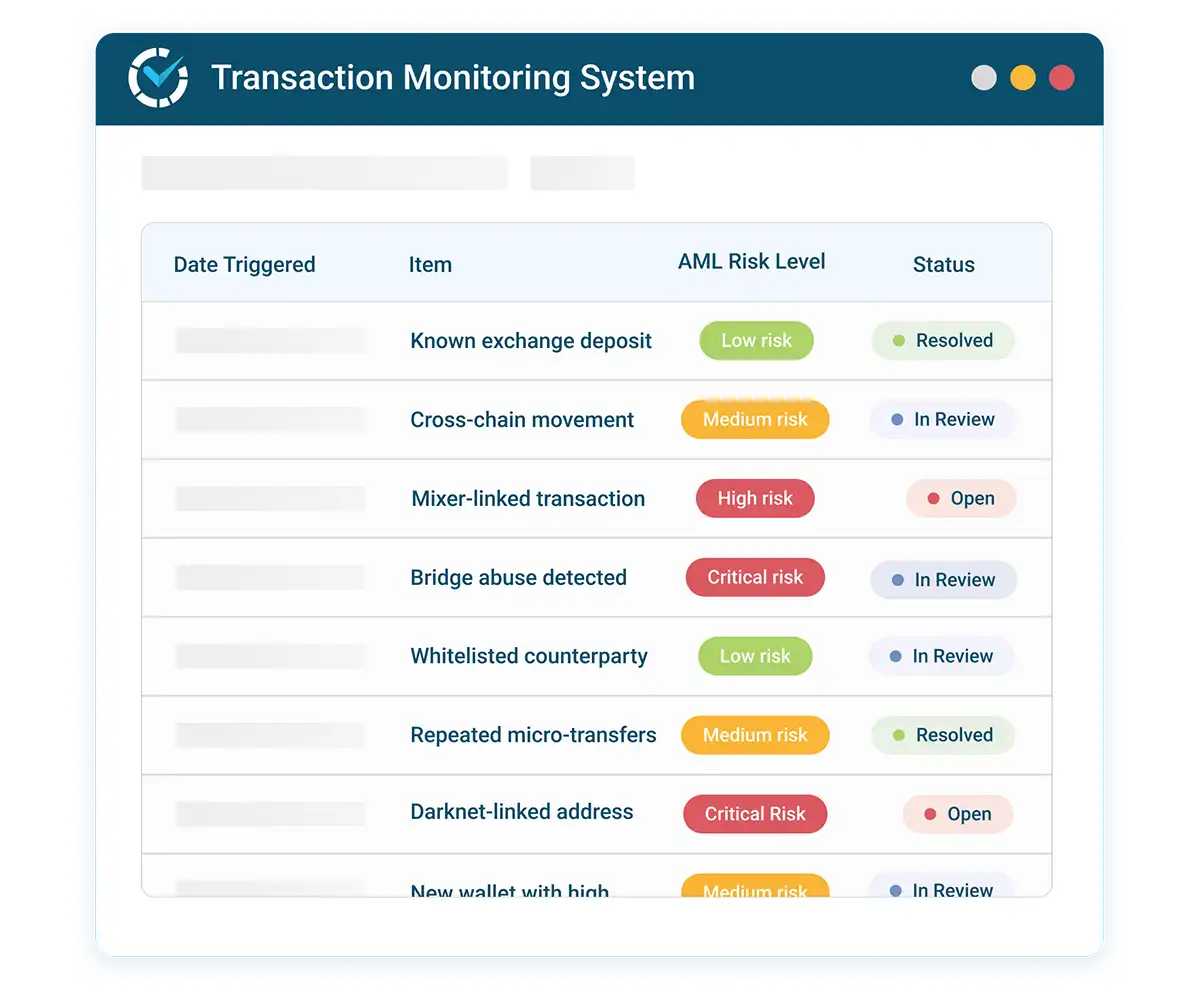
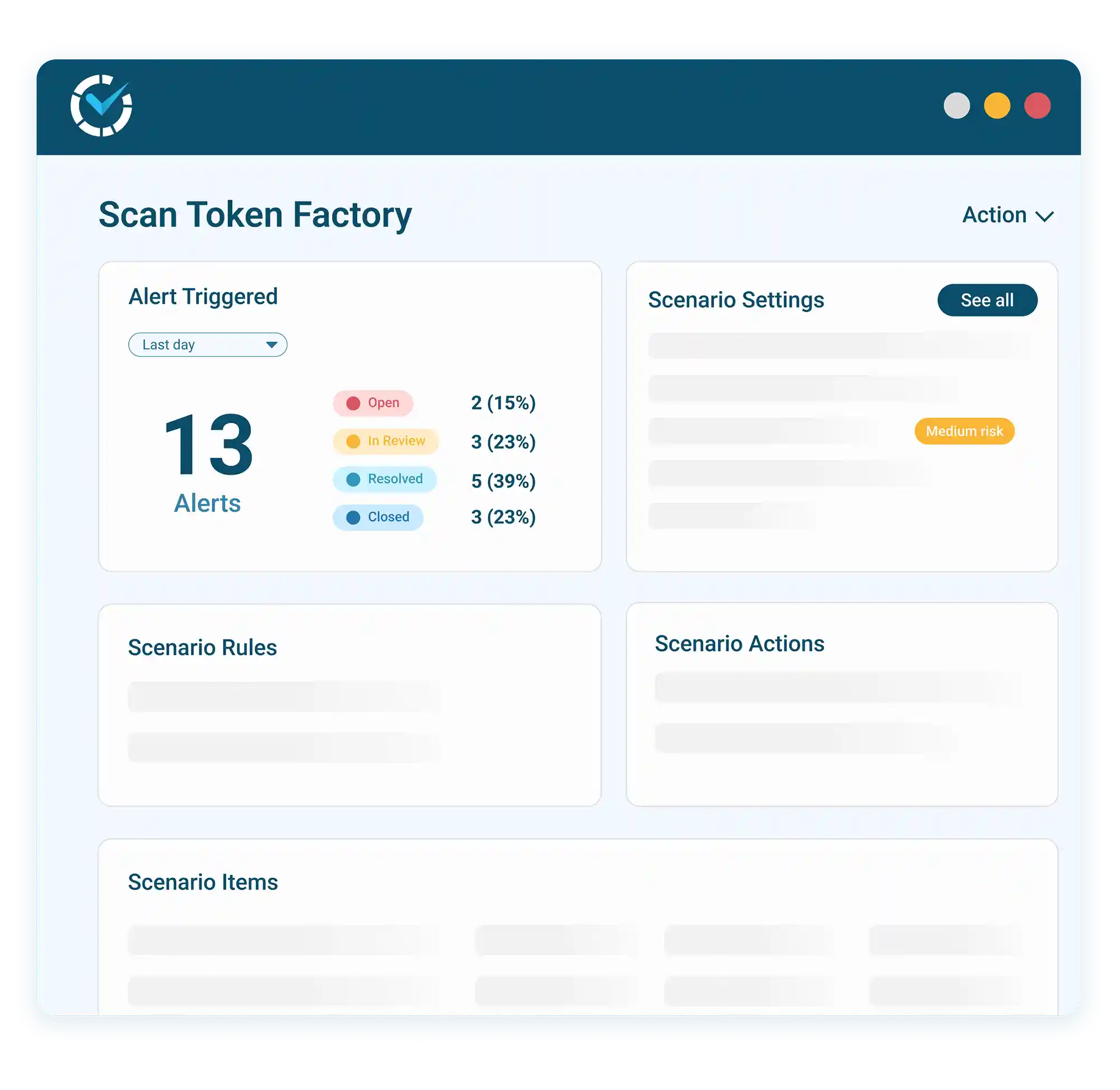
Real-Time Crypto AML Transaction Monitoring
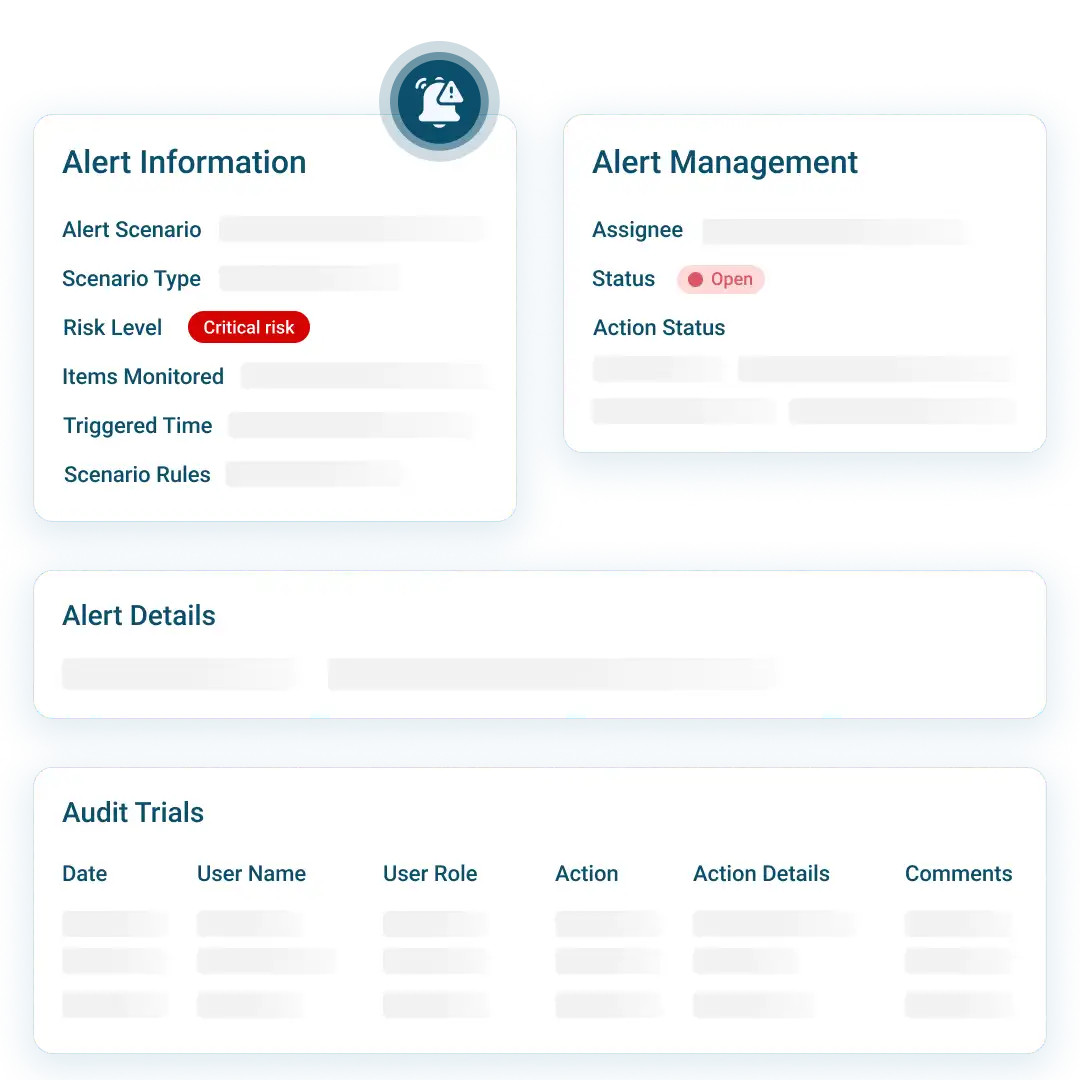
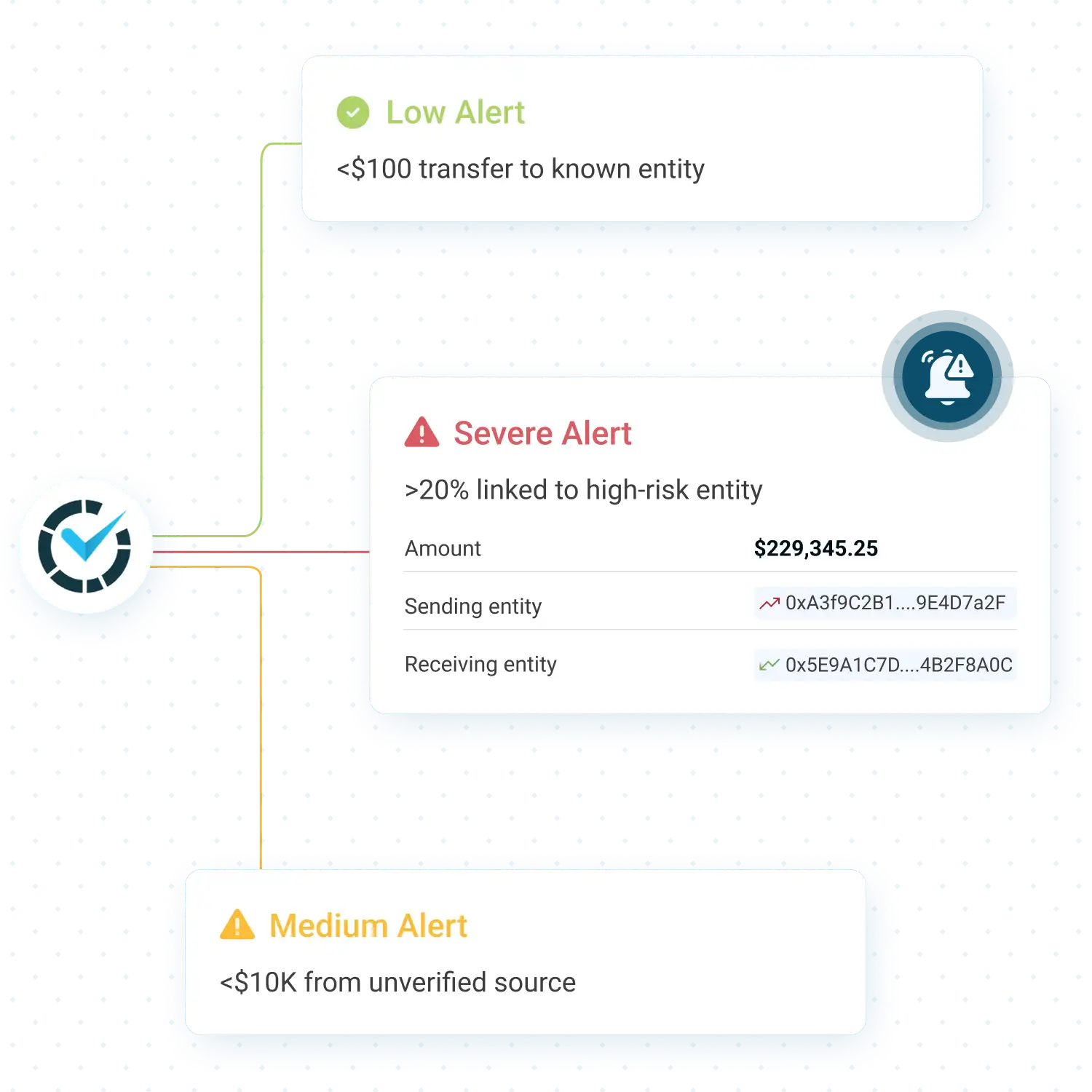
Continuously monitor on-chain activity using configurable, scenario-based risk logic.
Detect suspicious activity over time by applying real-time and periodic monitoring scenarios to on-chain transactions and wallets.